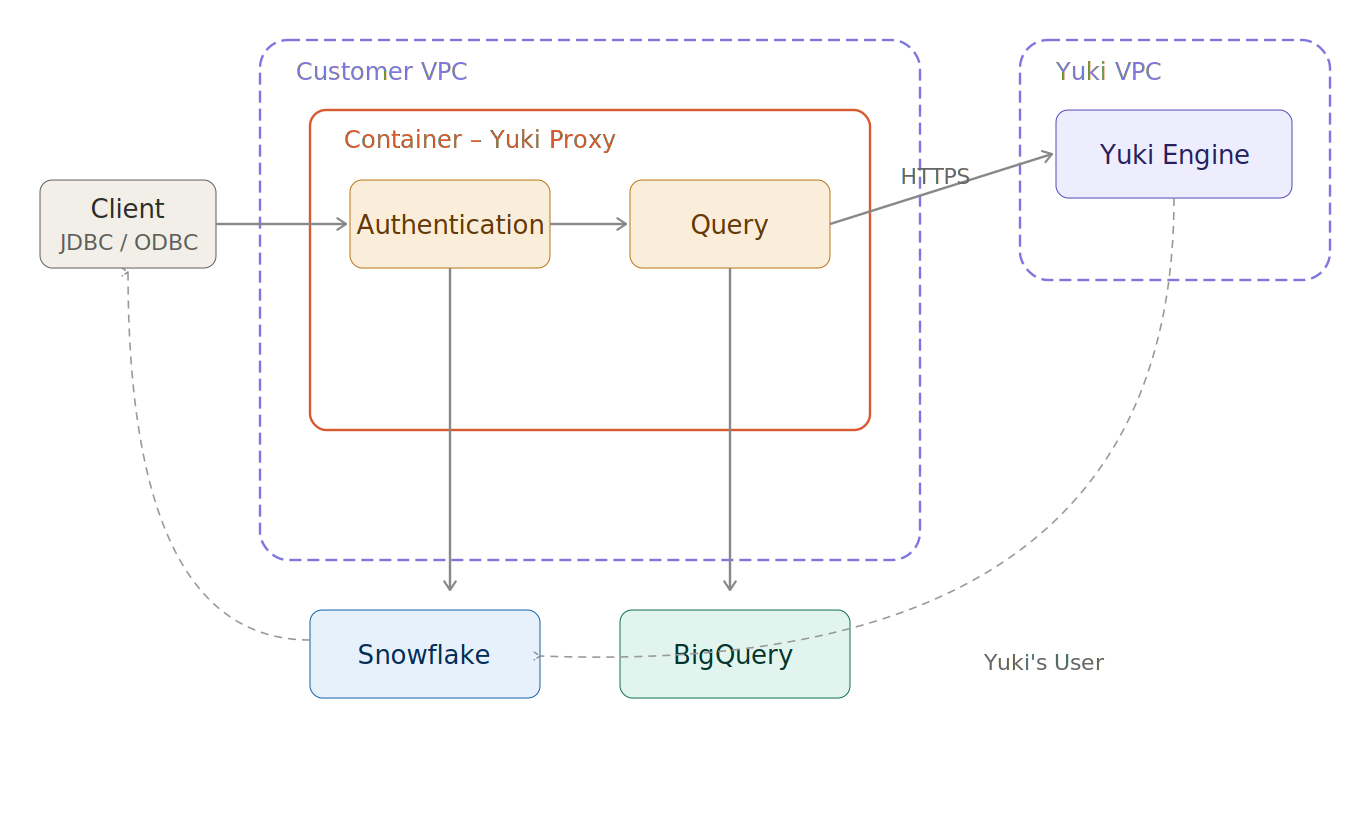
Secure Data Flow
Yuki's network design guarantees protected communications and comprehensive traceability through query processing. Data exchanges among customer systems, the Yuki Proxy, Yuki Engine, and your data platform feature encryption and authentication.
Authentication and Authorization
Snowflake
Initial operations use temporary tokens managed through Snowflake's native user and role structure.
- BI platform sends authentication request to Snowflake via Yuki Proxy
- Proxy transparently routes to Snowflake
- Snowflake manages authentication while preserving existing users, roles, and permissions
BigQuery
Initial operations use a dedicated service account with scoped IAM permissions.
- BI platform sends a query request via Yuki Proxy
- Proxy authenticates to BigQuery using the
yuki-saservice account credentials - BigQuery enforces existing IAM roles and project-level permissions
Each operation within Yuki services is authenticated and authorized using temporary tokens that can be invalidated upon request.
Query Encryption and Transmission
The Proxy applies SHA-256 encryption to query text, with keys stored in the customer's secret-management service. Encrypted queries travel securely over HTTPS using JWT tokens for Proxy–Engine authentication.
Compute Resource Allocation
Snowflake
The Engine analyzes workload and recommends appropriate warehouse resources. The Proxy adjusts session parameters and forwards queries to Snowflake.
BigQuery
The Engine analyzes workload and routes queries to the optimal BigQuery reservation and slot configuration. The Proxy forwards queries to the appropriate project and reservation.
Query Execution and Result Retrieval
Queries are processed under configured roles and permissions. Results return through the Proxy to the BI platform. Yuki retains no user data or query content post-execution.
Encryption in Transit
End-to-end HTTPS encryption protects all Yuki component communications using strong TLS standards across all connections.
Deployment Options
The same security principles apply across all deployment models:
| Model | Snowflake | BigQuery |
|---|---|---|
| Fully Hosted (SaaS) | ✓ | ✓ |
| Customer-hosted Proxy | ✓ | - |
| AWS PrivateLink | ✓ | - |